WordPress is a content management system for over 70 million sites. The malware only affects “Self-hosted” websites that use WordPress. Personal blogs on WordPress.com do not appear to be affected at this stage.
The plug in has several vulnerabilities, one of them allows anyone to upload a theme onto the site; this is then leveraged by the hackers to obtain control of the website. Previous malware attacks have been seen to use a worm that self-replicates; this is not the case with the Soak Soak attack, this malware appears to scan, looking for vulnerable hosts.
What should be done?
Any WordPress websites running an older version of the third party plug in, should be updated. The open source WordPress projects have created automatic updates for security fixes in the core WordPress application since version 3.7. The auto updates however, do not currently include updates for all user plug ins.
The effective deployment of Web Application Firewall rules are a key feature in minimising the risk. Latest WordPress releases provide users with a list of plug-ins that need to be updated within the dashboard area.
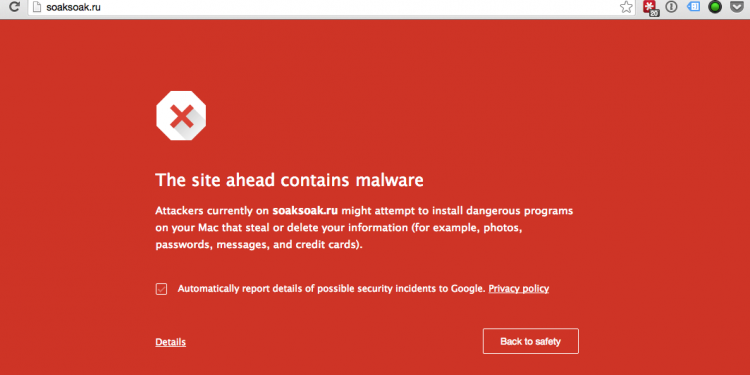
You can check the Google blacklisting status and whether or not a site is infected with malware using Sucuri’s site check tool. Sucuri also has a blog that will run you through what to do if your site is infected. Rest assured that IT West WordPress websites have been checked and upgraded where necessary. If you have any concerns about your website please do not hesitate to get in touch.